“The landing zone is a cloud environment that offers a recommended starting point, including default accounts, account structure, network and security layouts, and so forth. From a landing zone, you can deploy workloads that utilize your solutions and applications.” –
The AWS User Guide
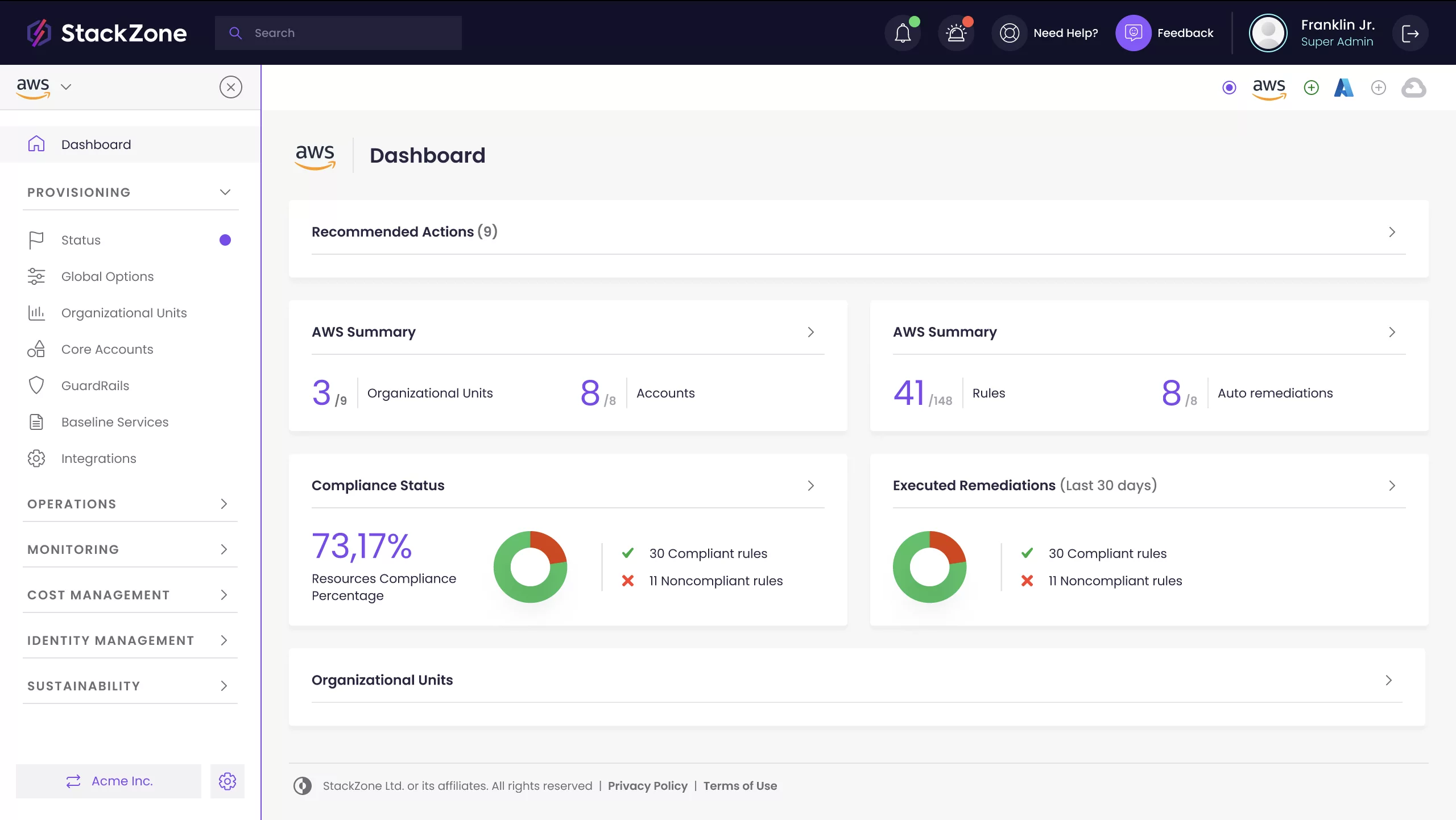
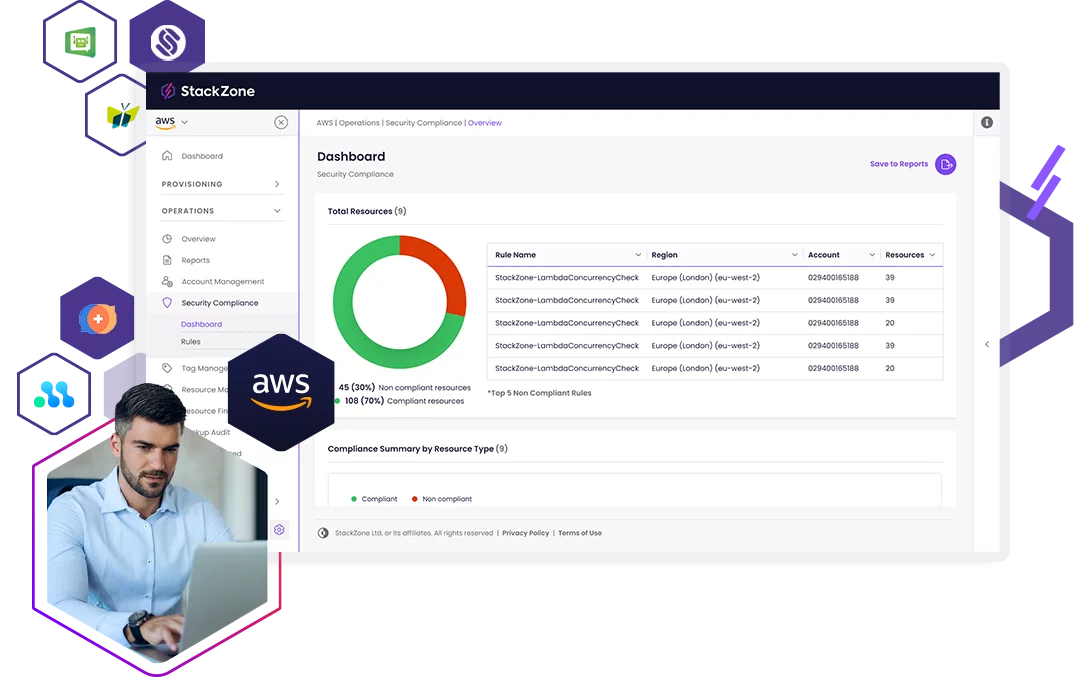
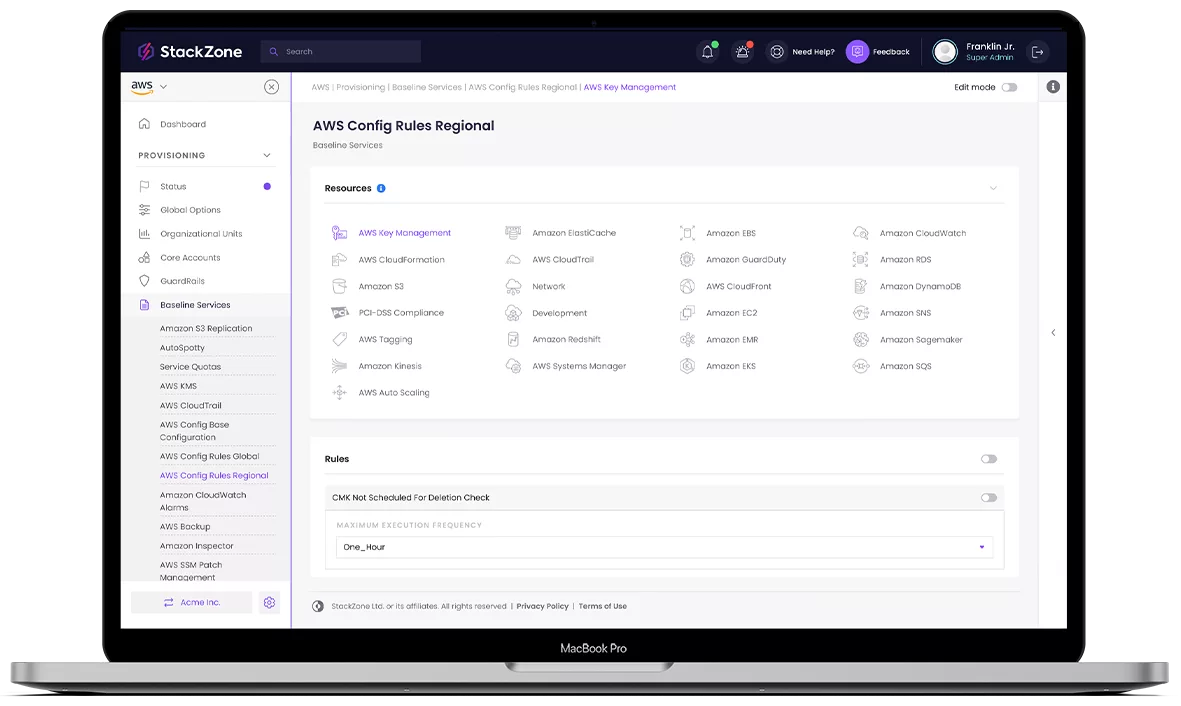
StackZone upholds and drives a multi-account strategy. Our AWS security tool simplifies landing zone management and access deployment. By separating your workloads into different accounts, your AWS environment becomes more scalable and secure. Ensure one compromised account doesn’t infect your entire cloud environment, causing complete downtime. Securely deploy appropriate access to accounts in a few clicks based on a user’s needs and role responsibilities. Isolate data to prevent unauthorised exposure with StackZone.